Analysis
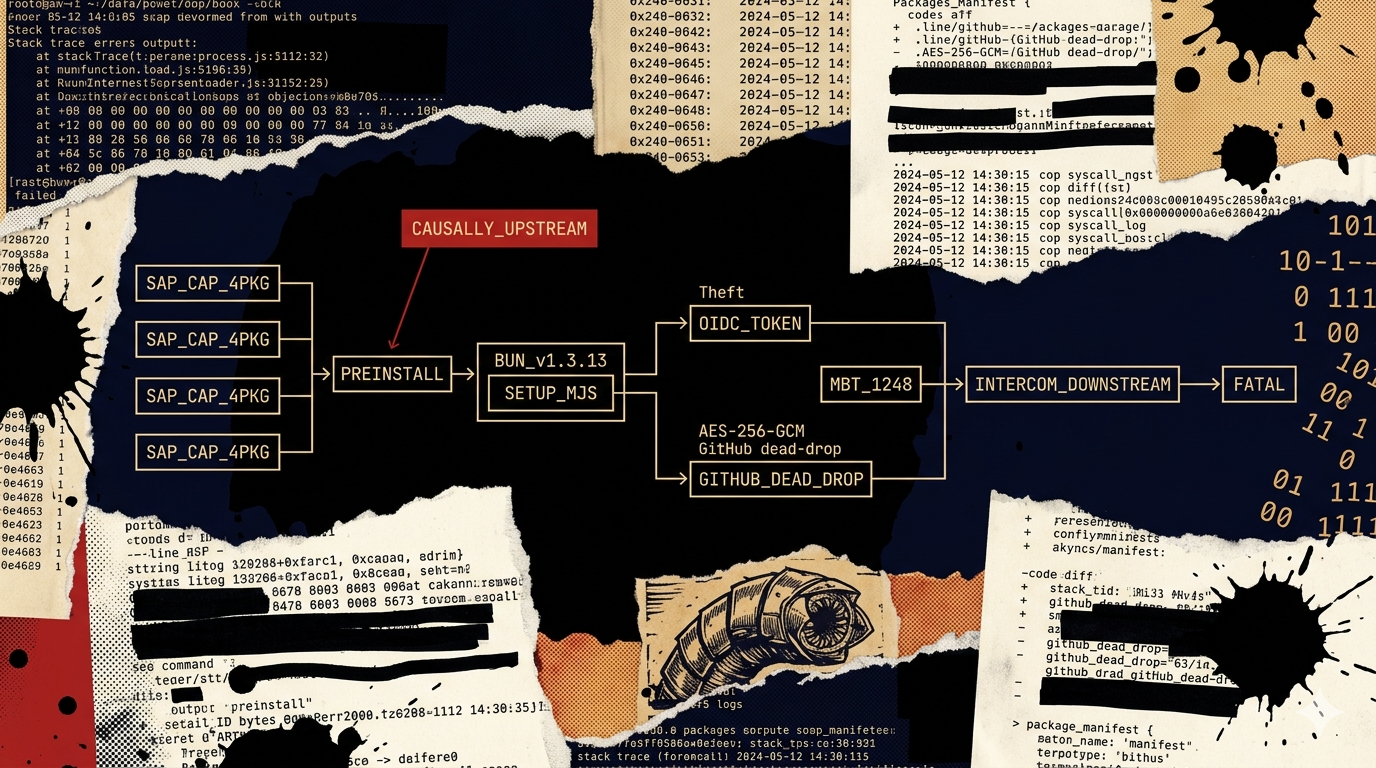
Four SAP Cloud Application Programming Model npm packages were published with malicious versions on April 29, 2026: @cap-js/sqlite v2.2.2, @cap-js/postgres v2.2.2, @cap-js/db-service v2.10.1, and mbt v1.2.48. The operator named the campaign in the exfil repository description: "A Mini Shai-Hulud has Appeared." Aikido Security published the primary analysis the same day.
This finding documents Mini Shai-Hulud as a standalone event, not as a footnote in the intercom-client story. The intercom-client compromise (Shai-Hulud, April 30) is covered separately. The two events are causally linked: GitHub Actions OIDC tokens stolen from mbt@1.2.48 on April 29 were used to publish the malicious intercom-client@7.0.4 on April 30. Mini Shai-Hulud is the upstream event.
Two things make Mini Shai-Hulud the pivotal finding in the cluster:
- Bun v1.3.13 is confirmed. Aikido's primary analysis explicitly identifies Bun v1.3.13 in
setup.mjs. This closes the open question in the npm worm cluster article: the v1.3.13 pin is a confirmed Layer 1 linking artifact connecting Mini Shai-Hulud, Shai-Hulud, and the TeamPCP toolkit. - The propagation marker is documented.
OhNoWhatsGoingOnWithGitHub— the string the worm uses to locate previously-stolen tokens in GitHub commit messages — is a detection artifact not previously recorded in any hub finding. This is how the worm finds credentials left by earlier victims to extend its reach.
What we know
- April 29, 2026 — four SAP CAP npm packages published with malicious versions. Aikido Security primary analysis published the same day.
- Naming: exfil repositories carry the description "A Mini Shai-Hulud has Appeared" — operator self-attribution consistent with the Dune-themed campaign branding across the cluster.
- Causal link to Shai-Hulud: Datadog Security Research notes that
mbt@1.2.48and@cap-js/sqlite@2.2.2are the earlier victims whose stolen OIDC tokens enabled the intercom-client hijack on April 30. The worm propagated from SAP CAP to Intercom in under 24 hours.
Why SAP CAP was targeted
SAP Cloud Application Programming Model is an enterprise Node.js/Java framework used in organizations running SAP Business Technology Platform. The ecosystem profile differs from the ML/AI credential surface targeted in litellm and lightning:
- Enterprise cloud credentials with broad scope. SAP CAP deployments on BTP hold credentials for AWS, Azure, and GCP service integrations alongside SAP-specific service bindings. CI/CD pipelines for SAP projects carry the same credential surface as any enterprise cloud-connected pipeline.
- npm publish tokens in enterprise CI/CD. SAP CAP projects use npm for package management. Development pipelines hold npm tokens with publish scope — the exact token class the worm uses for propagation.
- GitHub Actions OIDC tokens. SAP CAP projects hosted on GitHub using Actions-based CI/CD produce short-lived OIDC tokens that can be exchanged for npm publish credentials. The worm specifically targets these tokens:
mbt@1.2.48's stolen OIDC token was used to publishintercom-client@7.0.4. - AI/ML tooling now in enterprise contexts. The collection scope includes MCP server configuration files and Claude API tokens — reflecting that the operator updated their credential sweep to target AI engineering tooling now present in enterprise developer environments.
Payload mechanics
The following analysis is from Aikido Security's primary report, as characterized by Datadog Security Research.
Stage 1 — setup.mjs: The bootstrapper runs via a preinstall hook, detects OS and architecture, downloads Bun v1.3.13 from GitHub, and invokes execution.js under the Bun runtime. The explicit version pin v1.3.13 is the same pin used in the Shai-Hulud intercom-client@7.0.4 payload — confirmed Layer 1 linking artifact.
Stage 2 — execution.js: An 11.7 MB obfuscated JavaScript payload using a custom string scrambling layer labeled ctf-scramble-v2. This label is a new Layer 1 artifact: it is the operator's internal identifier for their obfuscation layer. The payload:
- Checks for Russian locale settings — exits if detected
- Detects whether it is running in CI — daemonizes itself on non-CI machines for persistent harvesting
- Forks a detached child process with
__DAEMONIZED=1to break process-tree correlation withnpm install
Collection scope — the payload harvests a broader credential surface than earlier TeamPCP PyPI victims:
- GitHub tokens (including output from
gh auth token) and npm tokens from.npmrc - GitHub Actions secrets — an embedded Python helper reads
/procmemory of theRunner.Workerprocess to extract secrets that are not written to disk - AWS STS identity, Secrets Manager secrets, and SSM Parameter Store parameters
- Azure subscriptions, Key Vault names, and Key Vault secret values
- GCP project identity and Secret Manager values
- Kubernetes service account tokens
- MCP server configuration files and Claude API tokens — new collection target in this payload; the operator has updated the credential sweep to include AI development tooling
- Azure token caches, GCP token databases, Signal configuration, Electrum wallets, VPN configuration files
The GitHub Actions Runner.Worker memory read deserves specific attention. GitHub Actions secrets are designed to never appear in logs — they are redacted. But the runner process holds them in memory. A Python helper that reads /proc/[pid]/mem of the runner process can extract secrets that the GitHub Actions security model explicitly assumes are not accessible. This is not a GitHub vulnerability — it is a privileged code execution on the runner extracting in-memory data. The defense is preventing the malicious code from executing, not hardening secret redaction.
Exfiltration: The malware creates public GitHub repositories with randomized names and the description "A Mini Shai-Hulud has Appeared". Stolen data is written as AES-256-GCM encrypted files under results/results-<timestamp>-<counter>.json, with the AES session key wrapped under an embedded RSA public key. All exfil traffic goes to api.github.com.
Propagation mechanism: The worm propagates via two paths:
- GitHub commit dead-drop discovery. The malware searches GitHub commit messages for the string
OhNoWhatsGoingOnWithGitHub. Matching commits contain base64-encoded GitHub tokens left by prior victims. The worm decodes and uses these tokens to access additional repositories — this is how the worm grows its token pool without direct C2 communication. - Package tarball injection. When the worm detects a GitHub Actions release workflow for
cap-js/cds-dbs, it modifies the package tarball to inject a maliciouspostinstallhook, increments the patch version, and repacks. It also pushes files into repositories under.vscode/and.claude/paths using commit messages titledchore: update dependencies— designed to blend into normal dependency maintenance commits.
Bun v1.3.13: cluster linking artifact confirmed
Observation: Aikido's primary analysis of Mini Shai-Hulud's setup.mjs identifies Bun v1.3.13 as the pinned version. The Shai-Hulud intercom-client@7.0.4 payload uses the same Bun v1.3.13 pin (confirmed in StepSecurity's primary analysis). The TeamPCP npm cluster analysis identified this pin as the proposed linking artifact but noted it required primary-source confirmation.
Mechanism: Pinning to a specific Bun point release is a deliberate build choice. v1.3.13 is not an LTS release, a current stable release, or a conventionally-adopted version. Independent codebases would not pin to the same non-current point release without coordinating on the same build system. The pin is reproducible only if both payloads originated from the same codebase — or from a codebase explicitly copying the pin.
Inference: Mini Shai-Hulud and Shai-Hulud share a build-time codebase. They are the same toolkit, not similar toolkits. The npm worm cluster linking artifact is confirmed at Layer 1.
Confidence bound: This would weaken if v1.3.13 were shown to be a widely-adopted convention in the npm malware ecosystem at the time — i.e., if other unrelated actors were independently pinning to this version. No evidence of that pattern exists.
Indicators of compromise
Compromised package versions:
@cap-js/sqlitev2.2.2@cap-js/postgresv2.2.2@cap-js/db-servicev2.10.1mbtv1.2.48
Filesystem artifacts:
setup.mjsin package root — bootstrapper; downloads Bun v1.3.13execution.jsin package root — 11.7 MB obfuscatedctf-scramble-v2payload- Bun v1.3.13 binary in a temp or hidden path
Network indicators:
- Outbound connection to GitHub API (
api.github.com) from npm install context — repository creation and commit operations not expected from package installation - Bun runtime download from GitHub during
npm install
GitHub artifacts:
- Public repositories with description "A Mini Shai-Hulud has Appeared" — operator self-attribution; any such repository in your GitHub org or fork network is evidence of worm activity
- GitHub commit messages containing
OhNoWhatsGoingOnWithGitHub— the propagation token marker; search your GitHub audit logs for this string - Commits with message
chore: update dependenciesadding files under.vscode/or.claude/paths — worm persistence injection
Campaign self-attribution:
- "A Mini Shai-Hulud has Appeared" — exfil repository description
ctf-scramble-v2— internal obfuscation layer label inexecution.js
Detection and mitigation
- Update all four packages immediately. The malicious versions are the only compromised releases. Any environment that ran
npm installwith these versions in the dependency tree should be treated as potentially compromised. - Search GitHub audit logs for
OhNoWhatsGoingOnWithGitHub. This string in any commit message in your organization's repositories is a worm propagation indicator. If found, the associated commit contains a base64-encoded stolen GitHub token — rotate all tokens in that repository. - Search for repositories with description "A Mini Shai-Hulud has Appeared". Any such repository under your organization or in your fork network was created by the worm's exfil routine.
- Rotate GitHub tokens, npm tokens, and all cloud credentials. The Runner.Worker memory extraction means secrets not written to disk may have been collected. Treat all CI/CD secrets from affected pipelines as compromised.
- Audit
.vscode/and.claude/for injected files. The worm pushes files into these paths as a secondary persistence mechanism. Any unexpected files in these directories committed by automated workflows warrant investigation. - Inspect MCP configuration and Claude API tokens. This is the first confirmed TeamPCP campaign to target MCP server configuration. If your CI/CD environment holds Claude API keys or MCP server definitions, rotate them.
- Detect Bun runtime download during npm install. Any process downloading Bun v1.3.13 from GitHub during
npm installis a worm indicator. This behavioral rule covers Mini Shai-Hulud, Shai-Hulud, and the broader TeamPCP toolkit.
Attribution and cluster position
Mini Shai-Hulud is the direct precursor to the Shai-Hulud intercom-client compromise. The causal chain is: Mini Shai-Hulud (April 29) steals OIDC tokens from mbt@1.2.48 → those tokens are used to publish intercom-client@7.0.4 (April 30, Shai-Hulud). The Bun v1.3.13 confirmation links both events to the TeamPCP toolkit. The operator named both with Dune-themed branding: Mini Shai-Hulud (SAP CAP precursor) and Shai-Hulud (intercom propagation).
See the npm supply-chain worm cluster analysis for the full cluster timeline and cross-campaign technical analysis. The Bun v1.3.13 confirmation documented here updates the cluster article's open question on the linking artifact.
Criminal-market signal
No dark-web presence for Mini Shai-Hulud tooling, the SAP CAP packages, or the "A Mini Shai-Hulud has Appeared" campaign infrastructure has been observed. The operator-run credential-collection model confirmed across the cluster applies. The MCP/Claude configuration targeting is consistent with an operator who uses the credentials directly — a commodity actor would not invest in targeting AI development tooling that requires context to exploit. H2 operator-run pattern confirmed.
